End-to-end encryption (E2EE) is a crucial security feature in the digital age, fundamentally changing how we communicate and protect our data. At its core, E2EE is a method of secure communication that ensures only the communicating users can read the messages they send or receive. This means that no third party, not even the service provider that facilitates the communication, can decipher the content. Understanding E2EE is increasingly vital as we rely more heavily on digital platforms for sensitive conversations, financial transactions, and personal information sharing.
The Pillars of End-to-End Encryption
End-to-end encryption operates on a foundation of robust cryptographic principles, meticulously designed to safeguard information from unauthorized access. The efficacy of E2EE hinges on two primary cryptographic mechanisms: asymmetric encryption and symmetric encryption, often used in conjunction to achieve both security and efficiency.
Asymmetric Encryption: The Key Exchange
Asymmetric encryption, also known as public-key cryptography, is the cornerstone of establishing secure communication channels. It utilizes a pair of mathematically linked keys for encryption and decryption: a public key and a private key.
Public Keys: Open Invitations to Encrypt
The public key is, as its name suggests, freely available to anyone. It can be shared openly without compromising security. When you want to send an encrypted message to someone, you use their public key to encrypt the message. This public key can encrypt messages, but it cannot decrypt them. Think of it like an open mailbox: anyone can drop a letter into it, but only the person with the key to the mailbox can open it and read the contents.
Private Keys: The Sole Decryption Authority
The private key, conversely, is kept secret by its owner. It is absolutely critical that this key remains confidential. The private key is used to decrypt messages that have been encrypted with the corresponding public key. So, in our mailbox analogy, the private key is the actual key that unlocks the mailbox. Even if someone intercepts the letter dropped into the mailbox (the encrypted message), they cannot read it without the private key.
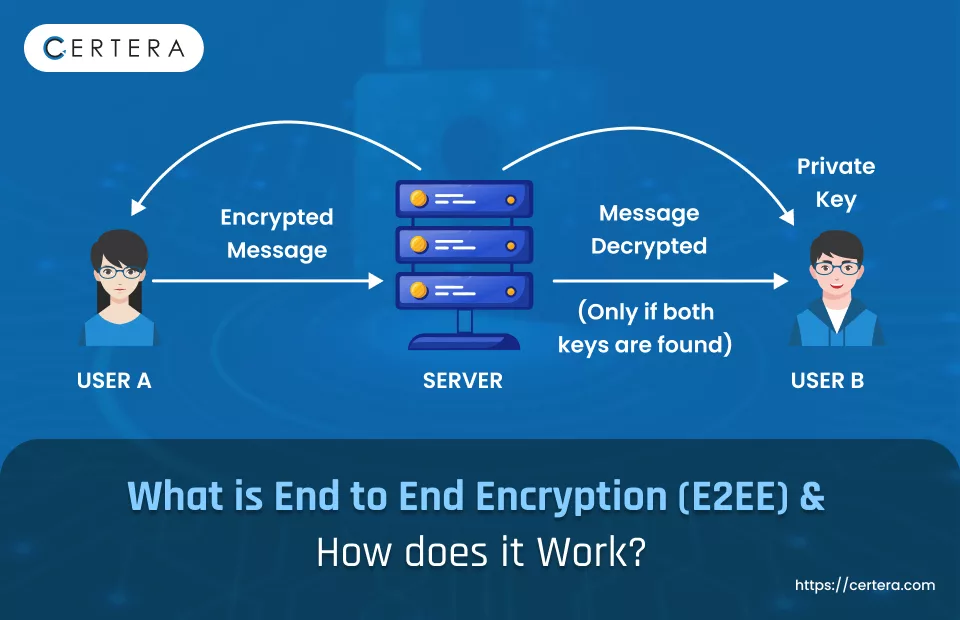
The secure exchange of public keys is paramount. When two parties initiate an E2EE conversation, they exchange their public keys. Once this exchange is complete, each party has the other’s public key and their own private key. This allows them to send secure messages to each other. For instance, if Alice wants to send a secure message to Bob, she will use Bob’s public key to encrypt her message. When Bob receives the encrypted message, he will use his private key to decrypt it, making it readable only to him.
Symmetric Encryption: The Efficiency Engine
While asymmetric encryption is excellent for securely exchanging keys, it can be computationally intensive for encrypting large amounts of data. This is where symmetric encryption comes into play. Symmetric encryption uses a single, shared secret key for both encryption and decryption.
The Shared Secret Key
In a symmetric encryption system, both the sender and the receiver possess the same secret key. This key is used to scramble the message (encrypt) and then unscramble it (decrypt). If the shared secret key is compromised, the security of the entire communication is lost.
The Hybrid Approach: Best of Both Worlds
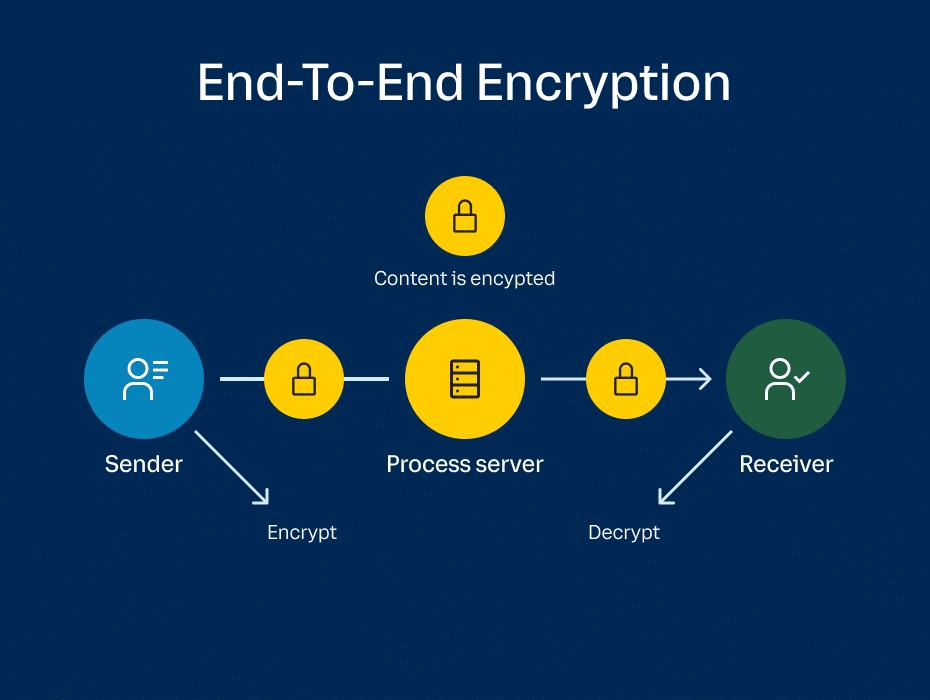
To leverage the strengths of both asymmetric and symmetric encryption, E2EE systems typically employ a hybrid approach. During the initial setup of a secure communication, asymmetric encryption is used to securely exchange a temporary, randomly generated secret key. This secret key is then used for symmetric encryption to encrypt the actual message content.
This hybrid method offers the best of both worlds: the secure key exchange provided by asymmetric cryptography and the speed and efficiency of symmetric cryptography for bulk data encryption. The entire process is transparent to the user, but it’s the underlying cryptographic ballet that ensures the security of their communications.
The Journey of an End-to-End Encrypted Message
To truly grasp the power of E2EE, let’s trace the journey of a message from sender to receiver, highlighting the cryptographic transformations and security layers involved. This journey illustrates the meticulous process that ensures privacy.
Initiation and Key Exchange
When you start a new chat session with someone on an E2EE-enabled platform, the first step is establishing a secure channel. Your device and the recipient’s device will perform an automated, secure key exchange. This typically involves using the asymmetric encryption methods discussed earlier. Your device generates a public and private key pair, and similarly, the recipient’s device does the same. Your public key is sent to the recipient, and their public key is sent to you. Crucially, your private keys never leave your respective devices.
Generating a Session Key
Following the public key exchange, a temporary, unique symmetric key, often called a “session key,” is generated. This session key is created randomly for each new communication session. To ensure that only you and your intended recipient can use this session key, it is encrypted using the recipient’s public key. When the recipient’s device receives this encrypted session key, it uses its private key to decrypt it. Now, both your device and the recipient’s device share the same, secret session key.
Encrypting the Message Content
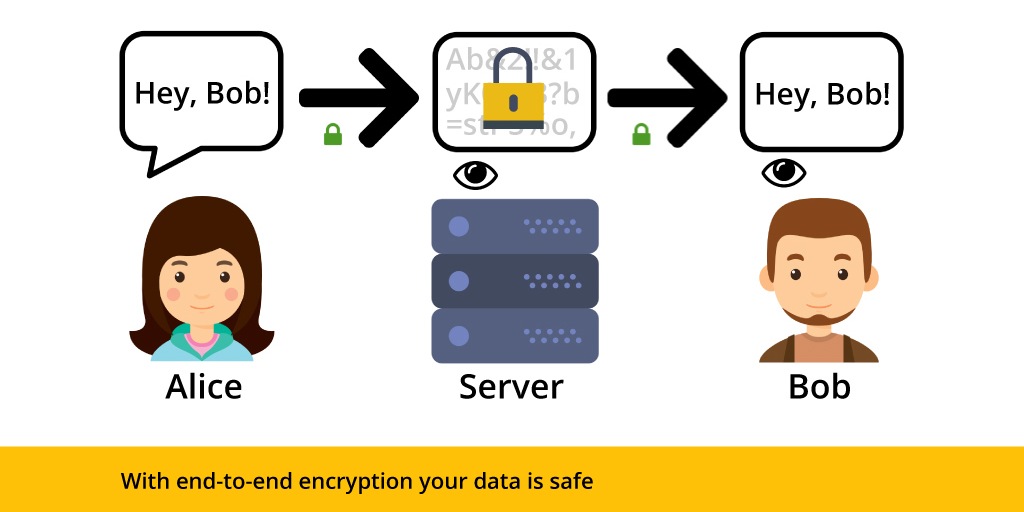
With the shared session key in hand, the actual message content is encrypted using symmetric encryption. This is a much faster process than asymmetric encryption. The message is scrambled into an unreadable cipher text. This cipher text is then transmitted over the network.
Transmission and Interception
The encrypted message travels across the internet. At this stage, any intermediary server or network provider that handles the message can only see the cipher text. They cannot read the actual content of the message. If a malicious actor were to intercept the transmission, they would only be able to access the scrambled data, which is useless without the corresponding session key.
Decryption at the Recipient’s End
When the encrypted message reaches the recipient’s device, it uses the shared session key (which it possesses) to decrypt the cipher text back into its original, readable form. This process is also handled by the symmetric encryption algorithm. The message is now visible to the intended recipient, and only to them.
This entire process, from key exchange to message decryption, happens instantaneously and automatically, creating a seamless and secure communication experience for the user. The complexity of the cryptography is hidden beneath a user-friendly interface.
The Significance of End-to-End Encryption in Modern Communication
End-to-end encryption is not merely a technical detail; it is a fundamental pillar of privacy and security in our increasingly interconnected world. Its implications extend across various aspects of our digital lives, safeguarding sensitive information and empowering individuals.
Protecting Sensitive Conversations
In an era where personal and professional exchanges often occur digitally, E2EE ensures that sensitive conversations remain private. This is particularly important for journalists communicating with sources, lawyers discussing confidential cases with clients, medical professionals sharing patient information, and individuals discussing personal matters. Without E2EE, these conversations could be vulnerable to interception by governments, corporations, or malicious actors, leading to potential blackmail, exposure, or misuse of information.
Ensuring Data Integrity and Confidentiality
Beyond just conversations, E2EE can be applied to various forms of data storage and transfer. For instance, encrypted cloud storage services utilize E2EE to protect your files from unauthorized access. Even if the cloud provider’s servers are compromised, your data remains secure as only you hold the decryption key. This is critical for businesses safeguarding intellectual property, individuals protecting personal documents, and anyone concerned about the confidentiality of their digital assets.
Building Trust in Digital Platforms
The implementation of E2EE by communication platforms and service providers is a significant signal of their commitment to user privacy. When users know that their communications are protected by E2EE, it fosters trust and encourages them to utilize these platforms for their most sensitive interactions. Conversely, the absence of E2EE can be a red flag, raising concerns about data security and potential surveillance.
Combating Surveillance and Censorship
E2EE plays a vital role in empowering individuals and communities in environments where surveillance and censorship are prevalent. By making communication content inaccessible to third parties, E2EE provides a crucial layer of protection against unwarranted monitoring. This enables free speech and the exchange of ideas without fear of reprisal, particularly important for activists, dissidents, and those living under authoritarian regimes.
The Future of Secure Digital Interactions
As technology continues to evolve, so too will the methods and applications of encryption. The ongoing development of more advanced cryptographic algorithms and protocols promises even greater levels of security. The widespread adoption and understanding of end-to-end encryption are essential for fostering a more secure, private, and trustworthy digital future, where individuals can communicate and share information with confidence, knowing that their data is protected from prying eyes.
