Simple Network Management Protocol (SNMP) is a foundational technology in network administration, allowing devices to communicate management information. Understanding the ports SNMP utilizes is crucial for effective network monitoring, configuration, and troubleshooting. While often operating silently in the background, these ports are the conduits through which vital network data flows, enabling administrators to maintain the health and performance of their infrastructure. This exploration delves into the specific ports associated with SNMP, their functions, and the security considerations that come with their usage.
The Core Ports of SNMP Operation
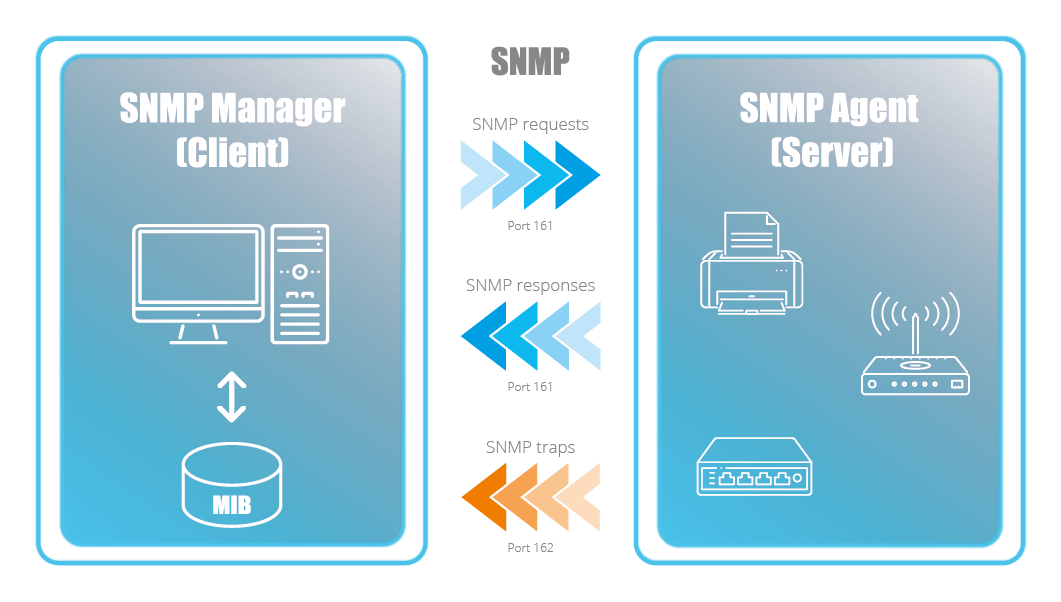
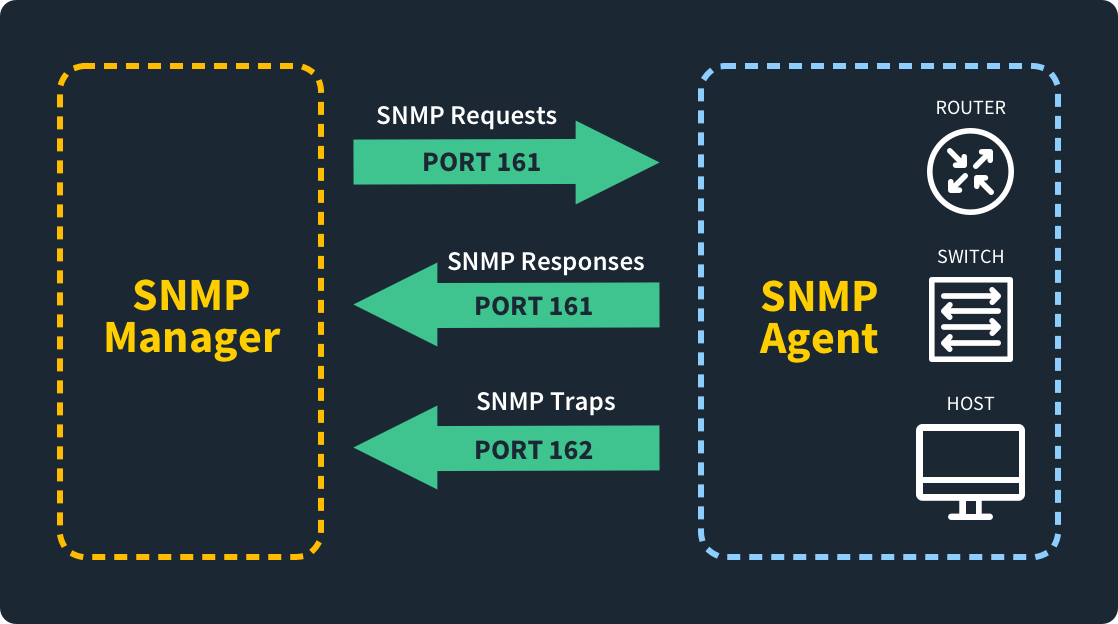
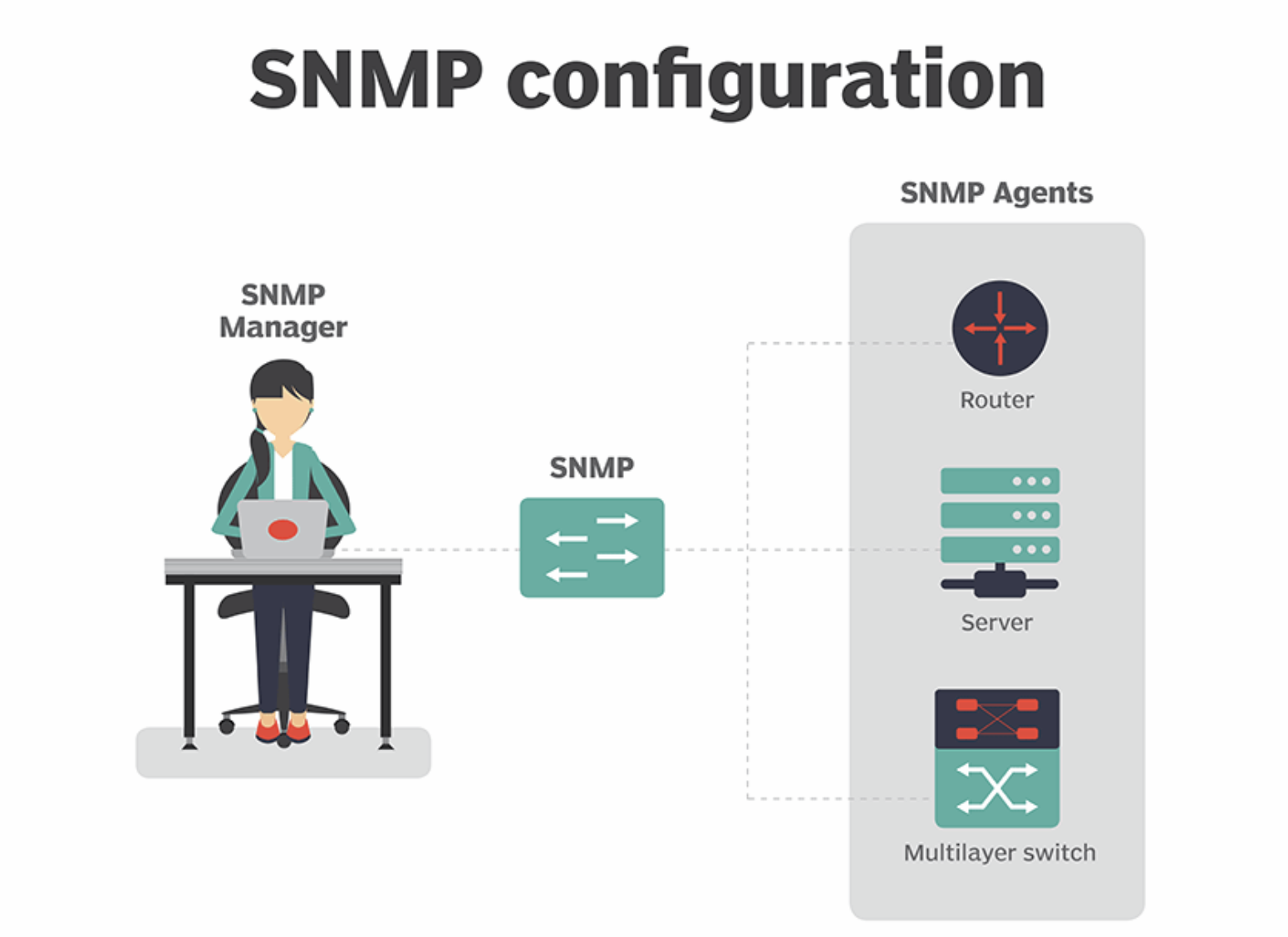
SNMP, at its heart, relies on a client-server architecture, with management stations (clients) querying managed devices (servers) for information or sending commands. This communication occurs over specific User Datagram Protocol (UDP) ports. Understanding these default ports is the first step in grasping SNMP’s operational mechanics.
UDP Port 161: The Primary Data Exchange Channel
The most critical port for SNMP is UDP port 161. This is the port on which SNMP agents, residing on managed devices such as routers, switches, servers, and even printers, listen for incoming requests from SNMP managers. When an SNMP manager needs to retrieve data, such as CPU utilization, memory status, or network interface statistics from a device, it sends a request to UDP port 161 on that device.
Conversely, if the SNMP manager needs to send configuration changes or set specific parameters on a managed device, these commands are also directed to UDP port 161. Essentially, UDP port 161 is the primary channel for both SNMP GET (retrieving information) and SNMP SET (modifying configuration) operations. The efficiency of UDP makes it suitable for this constant stream of management queries, as it offers lower overhead compared to TCP, which is beneficial for high-frequency data polling.
UDP Port 162: The Trap and Inform Listener
While UDP port 161 is for proactive queries initiated by the manager, UDP port 162 is dedicated to asynchronous notifications sent from managed devices (agents) back to the SNMP manager. These notifications are broadly categorized into two types: SNMP TRAPs and SNMP INFORMs.
SNMP TRAPs
SNMP TRAPs are unacknowledged messages sent by an agent to a manager to alert it to an event. These events could be critical, such as a device failure, a link going down, or a security breach. TRAPs are a one-way communication; the agent sends the trap, and the manager receives it without sending an acknowledgment. This makes TRAPs highly efficient for quickly alerting administrators to urgent situations without adding the overhead of confirmation.
SNMP INFORMs
SNMP INFORMs, introduced in SNMPv2, are similar to TRAPs in that they convey event notifications from agents to managers. However, INFORMs are acknowledged. When a manager receives an INFORM, it sends back a confirmation to the agent. This added reliability ensures that critical alerts are not lost in transit, making INFORMs more robust for situations where guaranteed delivery is paramount. Both TRAPs and INFORMs are sent to UDP port 162 on the designated SNMP manager or managers.
Beyond the Defaults: Customization and Security Considerations
While UDP ports 161 and 162 are the standard, network administrators often have the flexibility to reconfigure these ports for various reasons, primarily security. Deviating from default ports can be a tactic to obscure SNMP traffic from opportunistic attackers who specifically scan for these well-known ports.
Customizing SNMP Ports
In environments where enhanced security is a concern, administrators might choose to change the default UDP ports. For instance, an administrator might configure SNMP agents to listen on a non-standard port like 10161 for GET/SET requests and send traps/informs to a non-standard port like 10162. When this is done, it is imperative that the SNMP manager is also configured to poll and receive notifications on these custom ports.
This configuration change requires careful documentation and communication among network administrators. Failure to align the manager and agent port configurations will result in communication failures. However, the primary driver for this customization is to make SNMP traffic less visible to casual scans, thereby adding a layer of obscurity. It’s important to note that this is a form of “security through obscurity” and should not be the sole security measure employed for SNMP.
Security Implications and Best Practices
The default ports of SNMP, 161 and 162, are widely known and frequently targeted by malicious actors. Unsecured SNMP implementations can expose sensitive network information and even allow unauthorized control of devices. Therefore, robust security practices are essential when deploying SNMP.
SNMPv1 and SNMPv2c Vulnerabilities
Early versions of SNMP, specifically SNMPv1 and SNMPv2c, are inherently insecure due to their reliance on “community strings” for authentication. These community strings are essentially plain-text passwords. If an attacker gains knowledge of a community string, they can potentially:
- Read sensitive network information: By issuing GET requests with a valid read-only community string.
- Modify device configurations: By issuing SET requests with a valid read-write community string, potentially causing network outages or compromising device security.
- Exploit vulnerabilities: Some devices may have known vulnerabilities that can be triggered via SNMP.
Given these risks, using SNMPv1 and SNMPv2c without significant protective measures is strongly discouraged.
The Security Advancements of SNMPv3
SNMPv3 addresses the significant security weaknesses of its predecessors by introducing:
- Authentication: Ensures that messages originate from a legitimate source, preventing spoofing.
- Privacy (Encryption): Encrypts SNMP message content, making it unreadable to unauthorized parties.
- Integrity: Verifies that messages have not been tampered with in transit.
SNMPv3 supports different security levels:
- NoAuthNoPriv: No authentication or privacy (similar to SNMPv1/v2c’s basic functionality, but with a more structured framework).
- AuthNoPriv: Authentication but no privacy. This prevents spoofing and tampering but doesn’t protect the content of the messages.
- AuthPriv: Both authentication and privacy. This is the most secure option, offering strong protection against unauthorized access and eavesdropping.
When deploying SNMPv3, administrators configure users with specific credentials and security levels. The communication still happens over UDP ports 161 and 162, but the underlying security mechanisms protect the data traversing these ports.
Practical Security Measures for SNMP
Regardless of the SNMP version used, several practical measures can enhance security:
- Access Control Lists (ACLs): Configure firewalls and routers to restrict access to UDP ports 161 and 162, allowing connections only from trusted IP addresses or subnets (e.g., dedicated network management servers).
- Change Default Community Strings: If using SNMPv1/v2c, never use default community strings like “public” or “private.” Choose strong, complex, and unique community strings for each device or network segment.
- Use SNMPv3: Prioritize SNMPv3 for new deployments and migrate older devices to SNMPv3 if possible. Utilize the “AuthPriv” security level whenever feasible.
- Limit SNMP Agent Functionality: Configure SNMP agents on devices to only expose the necessary information and disable any read-write capabilities unless absolutely required.
- Monitor SNMP Traffic: Implement network monitoring solutions to detect unusual SNMP activity, such as excessive GET requests from unexpected sources or failed authentication attempts.
- Disable SNMP on Unmanaged Devices: If a device does not require SNMP management, disable the SNMP service entirely.
By implementing these security best practices, organizations can leverage the power of SNMP for network management while mitigating the associated risks.
Conclusion: The Essential Role of SNMP Ports in Network Management
The seemingly simple question of “what port does SNMP use” unlocks a deeper understanding of network management’s backbone. UDP port 161 serves as the primary conduit for querying and configuring network devices, while UDP port 162 facilitates crucial event notifications through TRAPs and INFORMs. The efficient, connectionless nature of UDP makes these ports ideal for the constant flow of management data.
However, the widespread adoption and the well-known nature of these default ports necessitate a strong focus on security. The evolution from the vulnerable SNMPv1 and SNMPv2c to the robust SNMPv3 has provided essential tools for authentication and encryption. Coupled with practical security measures like access control lists, strong community strings (for older versions), and judicious use of SNMPv3’s security levels, network administrators can effectively and securely harness the power of SNMP. Mastery of these ports and their associated security paradigms is not just a technical detail but a cornerstone of maintaining resilient, well-performing, and secure network infrastructures in today’s complex digital landscape.
