In the rapidly evolving landscape of unmanned aerial vehicles (UAVs), the focus is often placed on flight time, camera resolution, or obstacle avoidance sensors. However, the invisible tether that connects a pilot to their craft—the wireless communication link—is perhaps the most critical component of the entire drone ecosystem. As drones transition from hobbyist toys to professional tools used in inspections, search and rescue, and high-end cinematography, the security of this connection has become paramount. Central to this security is a protocol known as WPA2-PSK.
While many users recognize WPA2-PSK from their home internet settings, its implementation within drone accessories, controllers, and mobile applications is vital for preventing unauthorized access, signal hijacking, and data theft. This article explores the technical nuances of WPA2-PSK within the context of drone technology and why it remains the industry standard for securing the skies.
The Fundamentals of WPA2-PSK in Drone Communication
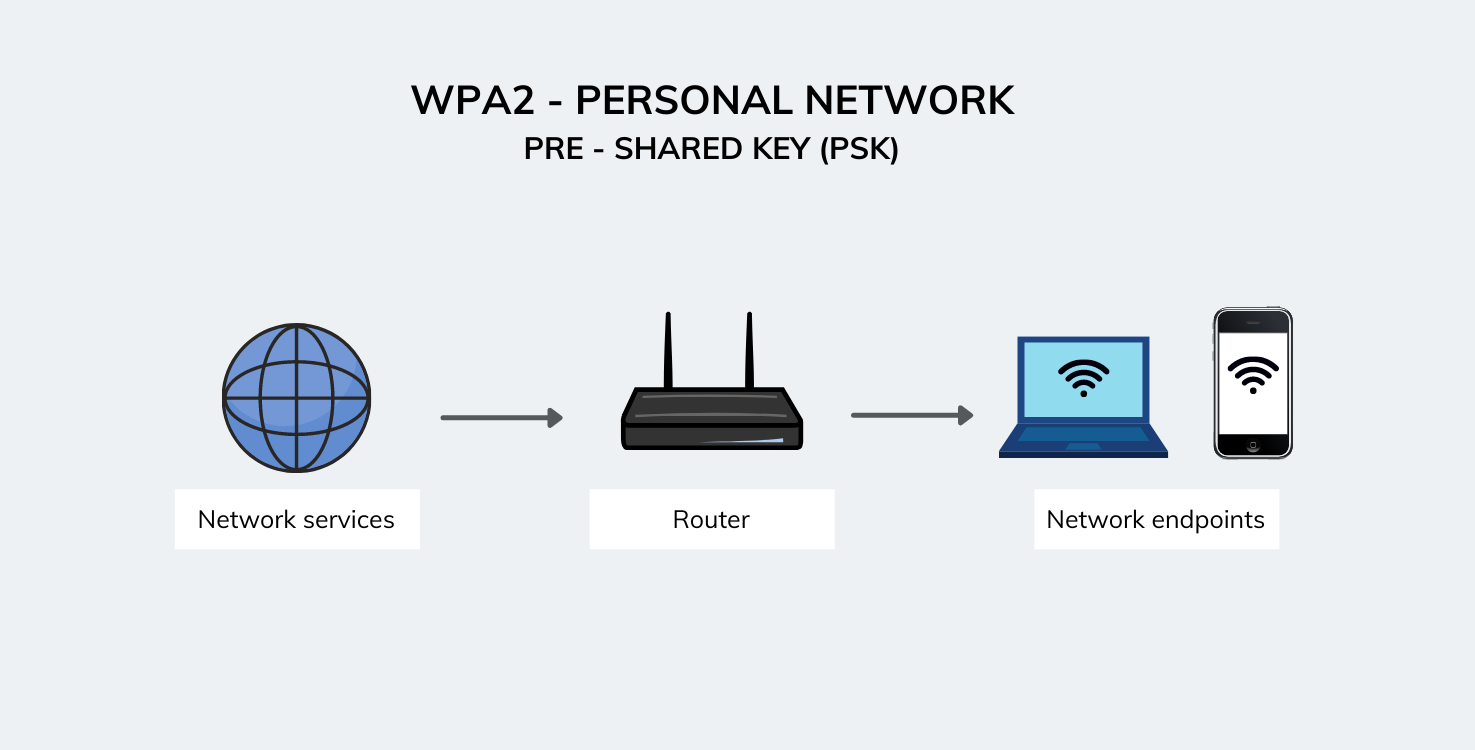
At its core, WPA2-PSK (Wi-Fi Protected Access 2 with Pre-Shared Key) is a security method used to encrypt data transmitted over a wireless network. In the world of drone accessories, this protocol is what secures the “hotspot” generated by a drone’s remote controller or the drone itself.
What is WPA2-PSK?
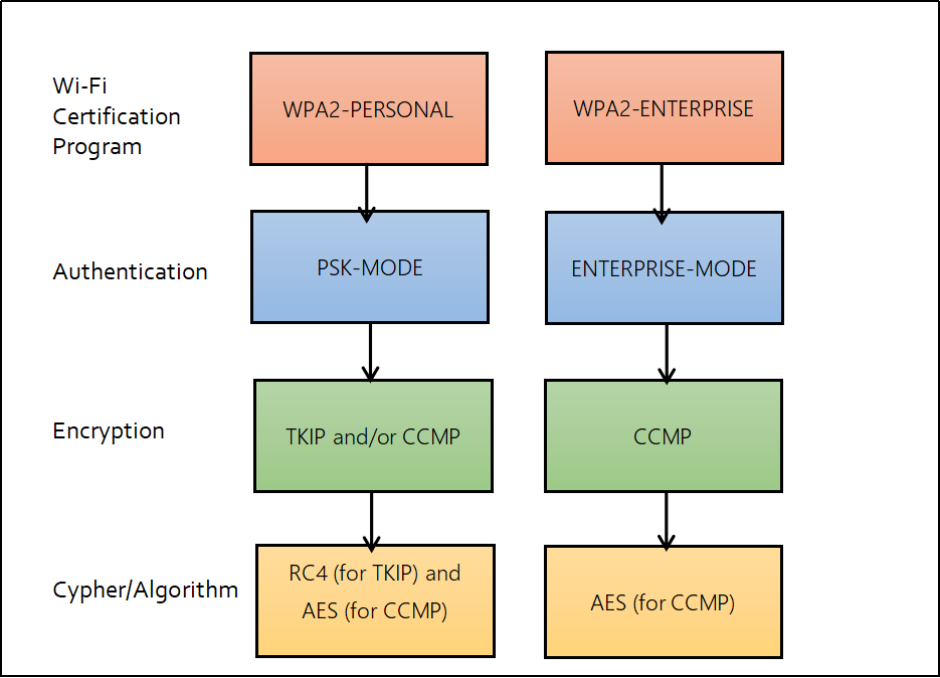
WPA2-PSK is a security certification program developed by the Wi-Fi Alliance to secure wireless computer networks. The “Pre-Shared Key” aspect refers to a static password or passphrase that both the drone (or controller) and the receiving device (such as a smartphone or tablet) must share to establish a connection. Unlike enterprise-level systems that use unique certificates for every user, PSK is designed for simplicity and efficiency, making it the ideal choice for field-deployed drone kits.
The protocol uses the Advanced Encryption Standard (AES), a 128-bit block cipher that is virtually uncrackable via brute force with current technology. When you power on a drone and connect your controller’s app via Wi-Fi, WPA2-PSK ensures that every packet of data—from your flight commands to the live video stream—is scrambled into a format that only the authorized receiver can decode.
Why Pre-Shared Key (PSK) Matters for UAVs
For a drone operator, the “Pre-Shared Key” is the first line of defense. When a drone creates its own Wi-Fi network to transmit a live 1080p feed to a smartphone, that network is visible to anyone within range. Without WPA2-PSK, any individual with a mobile device could theoretically “join” the drone’s network, gain access to the camera feed, or even attempt to inject flight commands.
By utilizing a PSK, the drone ecosystem creates a private, encrypted “tunnel.” This is particularly important for commercial operators who may be capturing sensitive data on industrial sites. The PSK ensures that even if a malicious actor intercepts the radio waves, the data within them remains unintelligible.
The Role of WPA2-PSK in Drone Accessories and Mobile Apps
Modern drones are rarely standalone units; they are part of a sophisticated network of accessories. This includes smart controllers, Wi-Fi range extenders, and mobile applications like DJI Fly, Autel Explorer, or Parrot FreeFlight. WPA2-PSK serves as the digital handshake that binds these accessories together.
Securing the Smartphone-to-Remote Connection
Many professional-grade drone controllers act as a bridge. The controller communicates with the drone via a proprietary long-range frequency (like 2.4GHz or 5.8GHz), but it communicates with the pilot’s tablet or smartphone via a localized Wi-Fi hotspot.
In this scenario, WPA2-PSK is active on the controller. When the pilot opens the drone’s app, the app searches for the controller’s encrypted SSID (Service Set Identifier). Without the correct WPA2-PSK credentials, the app cannot bridge the gap to the drone. This prevents a “man-in-the-middle” attack where a nearby observer could attempt to hijack the mobile device’s connection to the controller.
Protecting Telemetry Data and Live Feeds
The data flying through the air during a drone mission is highly valuable. Telemetry data includes the drone’s exact GPS coordinates, altitude, speed, and battery health. If this data were unencrypted, it would be easy for an adversary to track the drone’s home point or pinpoint the pilot’s location.
WPA2-PSK protects this telemetry stream. Furthermore, it secures the “First Person View” (FPV) video feed. For cinematic filmmakers or news organizations, protecting the intellectual property of the footage as it is being recorded is essential. WPA2-PSK ensures that the raw video being beamed to the ground station cannot be “sniffed” or recorded by unauthorized parties on the ground.
Comparing WPA2-PSK with Other Wireless Security Standards in Robotics
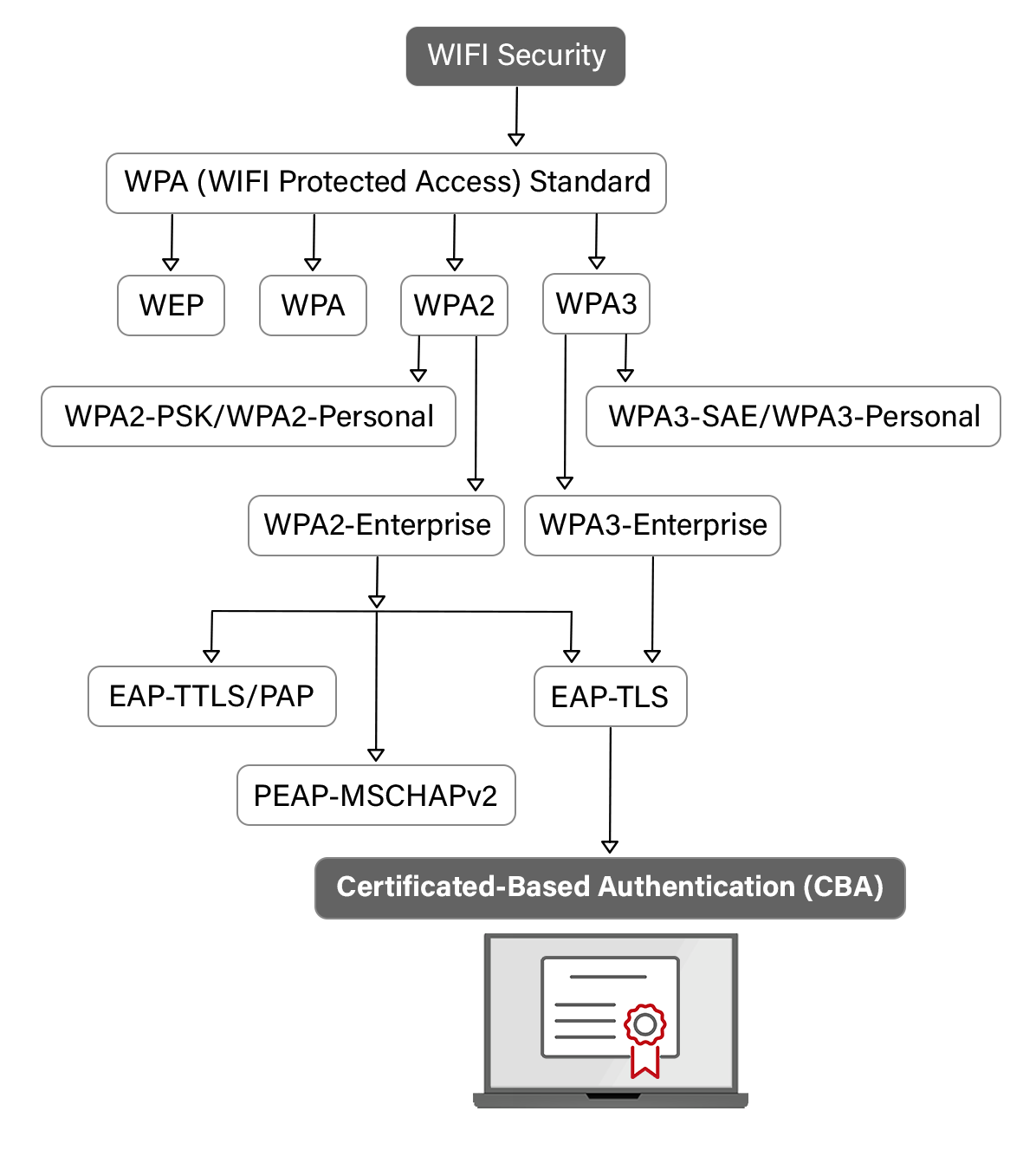
To appreciate the importance of WPA2-PSK, one must look at what preceded it and what is currently emerging. In the early days of consumer drones, security was often an afterthought, leading to significant vulnerabilities.
Why WEP and WPA are Obsolete for Modern UAVs
The predecessor to WPA2 was WEP (Wired Equivalent Privacy). WEP was notoriously weak; its encryption keys could be cracked in minutes using basic software available on a laptop. In the context of a drone, a WEP-secured connection would be an invitation for disaster, allowing hackers to potentially take control of the aircraft mid-flight.
WPA (the first version) improved upon WEP by introducing the Temporal Key Integrity Protocol (TKIP), but it still lacked the robust AES encryption found in WPA2. Modern drone manufacturers have entirely phased out WEP and WPA in favor of WPA2-PSK because the latter offers a much higher degree of computational security without requiring massive amounts of processing power—a crucial factor for battery-dependent drone accessories.
WPA2 vs. WPA3: The Next Frontier in Drone Security
As we look toward the future, WPA3 is beginning to appear in the latest high-end drone controllers. WPA3 improves upon WPA2-PSK by offering even better protection against “offline” dictionary attacks (where a hacker captures a handshake and tries to guess the password on their own computer).
However, WPA2-PSK remains the industry workhorse because of its backward compatibility. Many tablets and older smartphones used as monitors for drone flight do not yet support WPA3. For the foreseeable future, WPA2-PSK provides the best balance between universal compatibility with drone accessories and high-level security.
Implementation and Best Practices for Drone Operators
While WPA2-PSK is a robust protocol, its effectiveness is often limited by the “human element.” If an operator uses a weak password or fails to update their drone’s firmware, the security of the connection can be compromised.
Setting Up Strong Passwords for Drone Wi-Fi Hotspots
When a drone or controller comes out of the box, it often has a default SSID and password (e.g., “Drone12345”). Professional operators should change these immediately. A strong WPA2-PSK password should be at least 12 characters long and include a mix of uppercase letters, numbers, and symbols.
In the field, it might be tempting to use a simple password for ease of connection, but this creates a vulnerability. If you are operating in an urban environment or near a competing film crew, a weak password could allow someone to disrupt your signal or access your settings.
Avoiding Common Vulnerabilities in FPV and Consumer Drones
Many FPV (First Person View) racing drones use analog signals for video, which generally lack encryption. However, for digital FPV systems and standard consumer drones, WPA2-PSK is the primary defense. Operators should be wary of connecting their drone controllers to public Wi-Fi networks to download maps while the drone is active. This can create a path for malware to enter the drone’s control app.
Always ensure that your drone’s “Access Point” mode is configured to require WPA2-PSK. Some drones offer an “Open” mode for convenience; this should be avoided at all costs, as it transmits all data in the clear.
The Future of Encrypted Connectivity in Drone Ecosystems
As the drone industry moves toward beyond-visual-line-of-sight (BVLOS) operations and autonomous fleet management, the reliance on standard Wi-Fi protocols like WPA2-PSK is shifting toward integrated, hardware-level encryption.
AES Encryption and Hardware-Level Security
While WPA2-PSK handles the wireless handshake, many professional drones add an additional layer of AES-256 encryption directly on the hardware. This means the data is encrypted twice: once by the communication protocol (WPA2) and once by the flight controller itself. This “defense-in-depth” strategy is essential for government and enterprise drones where data integrity is a matter of national or corporate security.
Moving Beyond Wi-Fi: Long-Range Proprietary Links
While WPA2-PSK is the standard for the controller-to-mobile-device link, the link between the controller and the drone is increasingly moving toward proprietary systems like DJI’s OcuSync or Autel’s SkyLink. These systems often use techniques derived from WPA2-PSK but optimized for much longer distances and lower latency.
Even in these proprietary systems, the principles of the Pre-Shared Key remain. The “binding” process where you pair a new controller to a drone is essentially a sophisticated version of a PSK exchange. As drones become more integrated with the “Internet of Things” (IoT), the lessons learned from WPA2-PSK will continue to inform how we secure the airspace.
In conclusion, while WPA2-PSK might seem like a technical footnote in a drone’s spec sheet, it is the cornerstone of safe and private flight. By understanding how this protocol secures the link between drone accessories and apps, operators can better protect their equipment, their data, and the safety of the airspace in which they fly. Whether you are a cinematic filmmaker or an industrial inspector, the encrypted “handshake” of WPA2-PSK is what allows you to fly with confidence.
