Virtual Local Area Networks (VLANs) are a fundamental concept in modern network design, allowing for the logical segmentation of a physical network into multiple broadcast domains. This segmentation provides numerous benefits, including enhanced security, improved performance, and simplified network management. While the term “VLAN” might sound technical, its core purpose is to create isolated virtual networks within a single physical infrastructure, much like creating separate rooms within a larger building.
The Fundamental Concept of Network Segmentation
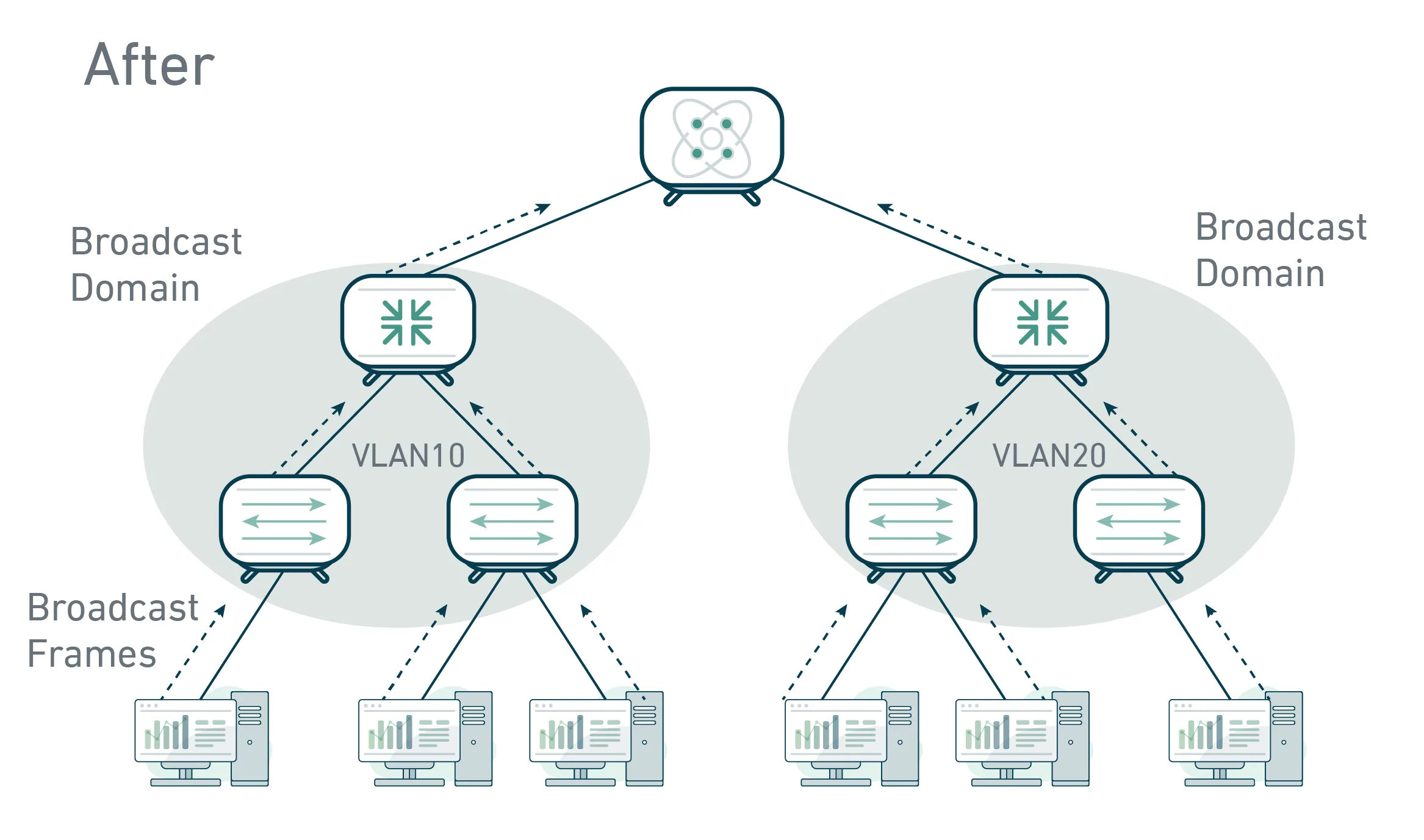
At its heart, a VLAN is a way to divide a single network switch into multiple smaller, independent networks. Traditionally, devices connected to the same switch would be part of the same broadcast domain. This means that when one device sent out a broadcast message (like a request to find an IP address), every other device on that switch would receive and process it. As networks grow, this can lead to significant network congestion and reduced performance, as devices are constantly bombarded with broadcast traffic they don’t need.

Understanding Broadcast Domains
A broadcast domain is essentially a network segment where broadcast packets are forwarded. In a traditional, flat network, the entire network is a single broadcast domain. When a device sends a broadcast, all other devices on the network receive it. This can be problematic because:
- Performance Degradation: With a large number of devices, broadcast traffic can consume a significant portion of network bandwidth, slowing down legitimate network traffic.
- Security Risks: Broadcast traffic can potentially expose sensitive information to unauthorized devices.
- Increased Processing Load: Every device has to process every broadcast packet, even if it’s not relevant to them, increasing CPU load on network devices.
The Role of Switches in Network Segmentation
Network switches are intelligent devices that learn the MAC addresses of devices connected to their ports. They use this information to forward traffic only to the intended destination port, rather than broadcasting it to all ports (as older hubs would do). However, even with switches, all devices connected to the same switch are still typically in the same broadcast domain. VLANs allow us to override this default behavior.
How VLANs Create Virtual Networks
A VLAN essentially tags network traffic. When a switch port is configured to be part of a specific VLAN, any traffic entering or leaving that port is marked with a VLAN identifier. This tag allows other switches on the network to understand which VLAN that traffic belongs to. As a result, broadcast traffic originating from a device in VLAN 10 will only be forwarded to other devices within VLAN 10, even if they are physically connected to different switches in the same network. This effectively creates separate, isolated broadcast domains.
Implementing VLANs for Enhanced Network Performance and Efficiency
The primary driver for implementing VLANs is to improve network performance and efficiency by reducing unnecessary broadcast traffic. By segmenting the network, we can isolate different types of traffic and user groups, ensuring that they do not interfere with each other.
Reducing Broadcast Traffic and Improving Bandwidth Utilization
Consider a large enterprise network with hundreds or even thousands of devices. Without VLANs, a single broadcast from one department could flood the entire network, impacting the performance of critical applications for all users. By creating VLANs for different departments (e.g., Sales, Engineering, Human Resources), broadcast traffic is confined to within each VLAN. This means that broadcasts from the Sales department will only be seen by other devices in the Sales VLAN, dramatically reducing the amount of traffic that needs to be processed by all devices on the network. This leads to:
- Lower Latency: Less congestion means data can travel faster.
- Increased Throughput: More bandwidth is available for actual data transfer.
- Smoother Application Performance: Mission-critical applications benefit from a more stable and predictable network environment.
Isolating Network Traffic and Improving Security
Beyond performance, VLANs are a powerful tool for enhancing network security. By segmenting the network, you can create virtual barriers between different groups of users or devices, limiting their ability to “see” or interact with each other’s traffic. This is crucial in environments with varying security requirements.
Segmentation by Department or Function
For example, you might create separate VLANs for:
- User Departments: Sales, Marketing, Finance, etc. This prevents users in one department from easily accessing resources intended for another.
- Servers: A dedicated VLAN for servers ensures that only authorized management traffic can reach them, and that server broadcasts are isolated.
- Printers and IP Phones: These devices often have specific traffic patterns and security needs.
- Guest Networks: A completely isolated VLAN for guest Wi-Fi access, ensuring that visitors cannot access internal company resources.
Limiting the Spread of Malware
In the event of a malware outbreak or a security breach, VLANs can act as a containment mechanism. If malware infects a device in one VLAN, it is much harder for it to spread to devices in other VLANs because the broadcast traffic carrying the malware is confined to its originating VLAN. This significantly reduces the attack surface and allows security teams to respond more effectively.
Simplifying Network Management and Administration
VLANs can also make network management more streamlined and efficient, especially in larger or more complex environments.
Logical Grouping of Devices
Instead of physically re-cabling the network to move a user or device to a different network segment, you can simply reassign their port to a different VLAN. This is particularly useful in organizations with mobile users or frequently changing departmental structures. For instance, if an employee moves from the Marketing department to the Sales department, their network access can be updated by simply changing the VLAN configuration on their network switch port, without needing to physically move any cables.
Easier Implementation of Policies
VLANs facilitate the implementation of network policies. For instance, you can apply Quality of Service (QoS) policies to prioritize certain types of traffic within a specific VLAN. Similarly, access control lists (ACLs) can be more granularly applied to traffic flowing between VLANs, further bolstering security. This allows administrators to define and enforce network rules on a per-VLAN basis, making it easier to manage and audit security settings.
Technical Implementation and Configuration of VLANs
Configuring VLANs involves understanding how switches handle tagged and untagged traffic and how these VLANs communicate with each other.
VLAN Tagging: The 802.1Q Standard
The most common protocol for implementing VLANs is the IEEE 802.1Q standard. This standard defines a method for tagging Ethernet frames with VLAN information. When a frame enters a trunk port (a port configured to carry traffic for multiple VLANs), a VLAN tag is inserted into the frame header. This tag includes a 4-bit VLAN ID (VID) which can identify up to 4096 VLANs (though some are reserved). This allows switches to differentiate between traffic belonging to different VLANs.
Access Ports vs. Trunk Ports
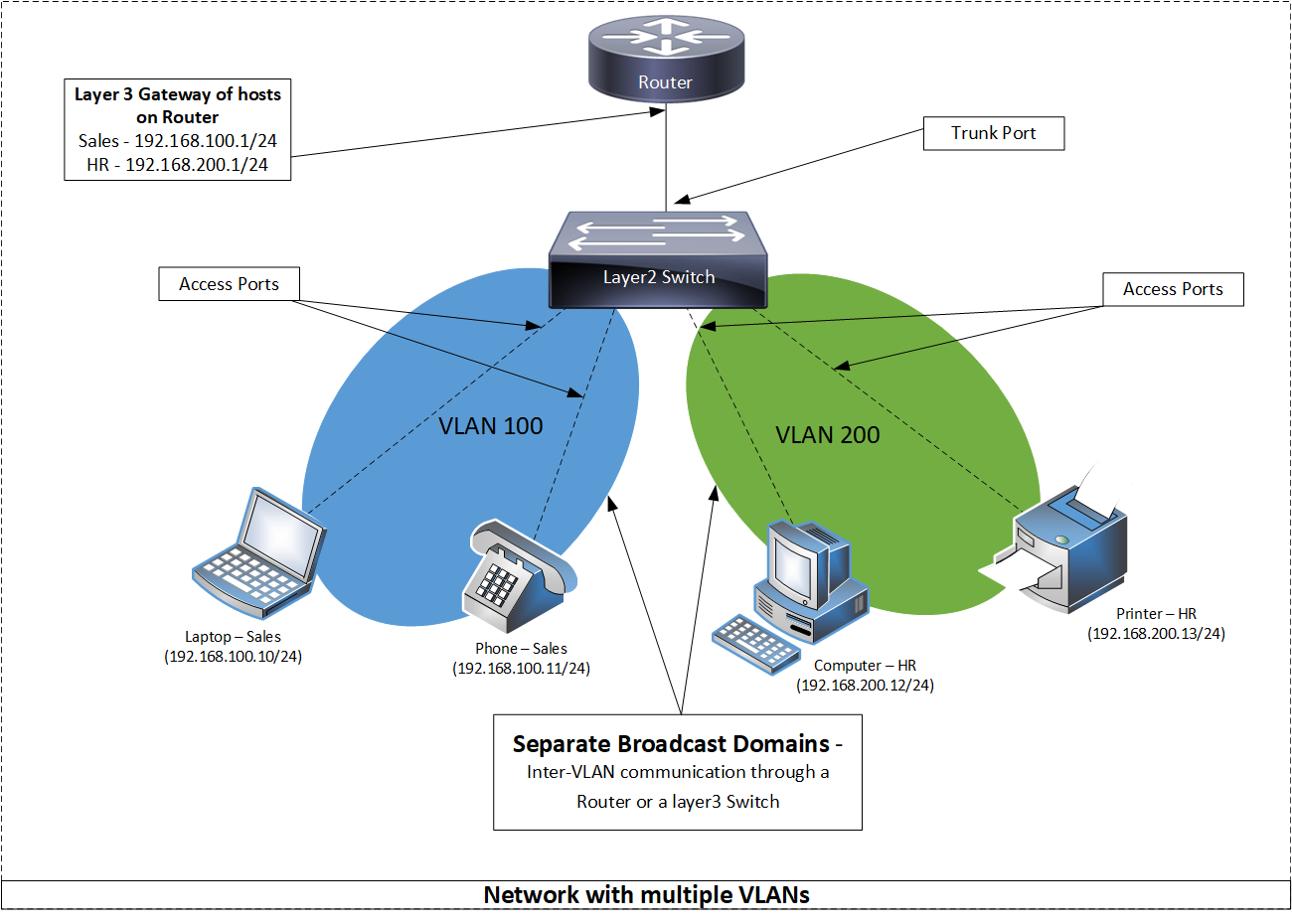
- Access Ports: These ports are typically connected to end devices such as computers, printers, or IP phones. Traffic entering an access port is usually untagged and is implicitly assigned to the VLAN configured on that port. When the switch sends traffic out of an access port, it removes the VLAN tag.
- Trunk Ports: These ports are used to connect switches to other switches or to routers. Trunk ports are configured to carry traffic for multiple VLANs and are responsible for preserving the VLAN tags. When a switch receives a frame on a trunk port, it forwards it to other trunk ports, maintaining the VLAN tag. This allows VLAN information to traverse the network infrastructure between switches.
Inter-VLAN Routing: Connecting Isolated Networks
By default, devices in different VLANs cannot communicate with each other. This is a deliberate security feature. If communication between VLANs is required, a mechanism known as “Inter-VLAN Routing” must be implemented.
The Role of Routers
Traditionally, routing between VLANs is handled by a router. Each VLAN is assigned a subnet (e.g., VLAN 10 might be 192.168.10.0/24, and VLAN 20 might be 192.168.20.0/24). The router has an interface or a virtual interface (called an “SVI” or Switched Virtual Interface on Layer 3 switches) connected to each VLAN. The router then acts as the default gateway for devices within each VLAN, forwarding traffic destined for other VLANs or the internet.
Layer 3 Switches
Modern networks often utilize Layer 3 switches, which can perform routing functions in addition to switching. These devices integrate routing capabilities directly, allowing for more efficient Inter-VLAN routing without the need for an external router in many cases. This can significantly improve performance as routing decisions are made at the switch level, closer to the end devices.
Managing VLANs: Tools and Best Practices
Effective VLAN management requires a systematic approach and the use of appropriate tools.
VLAN Naming Conventions and Documentation
Consistent naming conventions for VLANs are crucial for clarity. Instead of arbitrary numbers, VLANs should be named descriptively, such as “VLANSALES10,” “VLANENGINEERING20,” or “VLANGUEST50.” Comprehensive documentation detailing the purpose, assigned IP subnets, and associated devices for each VLAN is essential for troubleshooting and future planning.
Regular Audits and Security Reviews
Periodically auditing VLAN configurations and security policies is vital. This includes ensuring that ports are assigned to the correct VLANs, that trunk links are properly secured, and that Inter-VLAN routing rules are in place and enforced. Security reviews should focus on ensuring that the segmentation is achieving its intended security goals and that there are no unintended pathways for unauthorized access.
Advanced VLAN Concepts and Applications
Beyond the basic implementation, VLANs offer advanced capabilities that can further optimize network operations and security.
Voice VLANs and Quality of Service (QoS)
In modern communication systems, Voice over IP (VoIP) phones are a common sight. To ensure clear and uninterrupted voice calls, a dedicated Voice VLAN is often implemented. This VLAN prioritizes voice traffic, guaranteeing that it receives sufficient bandwidth and low latency. Quality of Service (QoS) policies are then applied to the Voice VLAN to ensure that voice packets are handled with the highest priority, even during periods of high network congestion.
Private VLANs (PVLANs)
Private VLANs add an extra layer of isolation within a single VLAN. While standard VLANs separate broadcast domains between VLANs, PVLANs can further segment devices within a single VLAN. This is useful in scenarios like service provider environments or large data centers where you might have multiple tenants or customers sharing the same physical infrastructure but requiring strict isolation from each other. PVLANs can have:
- Isolated Ports: Devices connected to isolated ports can only communicate with promiscuous ports.
- Community Ports: Devices connected to community ports can communicate with each other and with promiscuous ports, but not with devices on other community ports or isolated ports.
- Promiscuous Ports: These ports can communicate with all other ports in the PVLAN.
VLAN Hopping and Security Concerns
While VLANs enhance security, they are not foolproof. Sophisticated attackers may attempt “VLAN hopping” attacks, where they try to gain access to traffic in a VLAN they are not authorized to be in. Common VLAN hopping techniques include:
- Switch Spoofing: An attacker configures their machine to impersonate a switch and sends DTP (Dynamic Trunking Protocol) messages to the legitimate switch, tricking it into forming a trunk link.
- Double Tagging: This attack exploits how switches process 802.1Q tags. The attacker crafts a frame with two VLAN tags – an outer tag that matches the allowed VLAN on the trunk and an inner tag that matches the target VLAN. The first switch strips the outer tag, forwarding the frame to the next switch with only the inner tag, potentially allowing it to enter the target VLAN.
To mitigate these risks, best practices include:
- Disabling DTP on access ports.
- Explicitly configuring trunk ports and disallowing trunking on ports that don’t require it.
- Using the native VLAN feature with caution and not assigning sensitive traffic to the native VLAN.
- Regularly updating switch firmware to patch known vulnerabilities.
Conclusion: The Indispensable Role of VLANs in Modern Networking
Virtual Local Area Networks (VLANs) have evolved from a niche networking feature to an indispensable technology for any modern network, from small businesses to large enterprises and data centers. By enabling logical segmentation of physical networks, VLANs provide a powerful and flexible solution for enhancing performance, bolstering security, and simplifying network management. The ability to isolate broadcast domains, control traffic flow, and create distinct network segments without requiring physical re-cabling offers significant operational and cost efficiencies. As networks continue to grow in complexity and demand for robust security increases, understanding and implementing VLANs becomes paramount for network administrators seeking to build and maintain resilient, efficient, and secure network infrastructures.
